This section will describe the various types of Cisco Wireless architecture and AP mode. The Cisco Wireless Architecture provides connectivity between wired and wireless networks. There are different ways to connect wireless networks with the wired network using different types of Cisco Wireless Architecture.
What is Cisco Wireless Architecture
Cisco Wireless Architecture is a comprehensive solution for deploying and managing wireless networks. The solution consists of several components, including access points (APs), wireless controllers, and management software.
Access Points: Cisco access points are the devices that provide wireless connectivity to clients. They are available in various models, including indoor and outdoor, with different antenna types, and support for various wireless standards.
Wireless Controllers: Cisco wireless controllers are the devices that manage and control access points. They provide centralized management and configuration of the wireless network and allow for features such as roaming, security, and quality of service.
Management Software: Cisco provides management software that allows administrators to monitor and manage the wireless network. The software provides features such as reporting, troubleshooting, and policy management.
Different Types of Cisco Wireless Architecture
There are three different types of Cisco Wireless Architecture;
- Autonomous AP Architecture
- Cloud-based AP Architecture
- Split-mac Architecture
Autonomous AP Architecture in Cisco Wireless Architecture
- Autonomous access point (AP) architecture refers to a network design where each access point can operate independently without relying on a central controller. This allows for better scalability, as each AP can easily be added or removed from the network without affecting the entire system.
- Autonomous APs typically include their own management interface that allows for the configuration and monitoring of the AP. This type of architecture can also provide better reliability, as there are no single points of failure.
- Autonomous AP architecture offers fully functional basic service sets (BSS) that can be one or more than one.
- Basically, Autonomous APs provide connectivity between the service set identifiers (SSID) and wired VLANs at the access layer.
- The following figure describes the basic autonomous APs deployment for the enterprise network.

The network consists of a number of autonomous APs running two SSIDs namely: WLAN20 and WLAN 30.
- However, autonomous APs may not be as feature-rich as controller-based APs, which rely on a central controller to manage the entire network. Controller-based APs offer advanced features such as centralized management, traffic shaping, and more granular control over the network.
- Ultimately, the decision to choose autonomous or controller-based AP architecture comes down to the specific needs and requirements of the network.
Cloud-based Architecture in Cisco Wireless Architecture
Cloud-based wireless architecture is a network infrastructure where all the wireless networking services are centralized in the cloud by a service provider. This architecture typically consists of the following elements:
1. Cloud-based controller – A cloud-based controller is a software-based controller that is hosted in the cloud. It manages and configures the access points and other network components, providing centralized control for the entire network.
2. Access points – Access points are wireless devices that are used to provide wireless connectivity to users. They are typically managed by the cloud-based controller.
3. Cloud-managed switches – Cloud-managed switches provide connectivity between the access points and other network components. They are typically managed by the cloud-based controller as well.
4. Cloud-based analytics – Cloud-based analytics provide real-time reporting and analysis of network performance and user behavior.

The main characteristics of cloud-based architecture are as follows.
- The problem with the autonomous AP infrastructure is that when the number of AP increases, it is more cumbersome and critical to manage all the APs individually.
- This requires a central management platform through which all the APS can be managed automatically.
- The cloud-based architecture employs Cisco Prime Infrastue for efficient installation and management of autonomous AP.
- The administration of APs is shifted to a cloud-based platform for Cisco Meraki network devices provided by the Cisco Meraki cloud solution. The Cisco Meraki cloud provides an easier platform for deploying, installing, configuring, and managing the APs centrally and automatically.
- The dashboard is provided by Cisco Meraki Cloud for autoconfiguration of the APs. Before that AP must be registered with the Cisco Meraki cloud.
- The cloud-based wireless architecture enables you to quickly scale up or down your wireless infrastructure based on your business needs.
- A cloud-based wireless architecture provides the flexibility to deploy and manage your wireless network from anywhere, at any time.
- The cloud-based architecture eliminates the need for expensive hardware appliances and reduces the costs associated with maintenance and upgrades.
- Cloud-based wireless architecture provides advanced security features such as WPA3 encryption, rogue AP detection, and role-based access control.
Split-mac AP Architecture in Cisco Wireless Architecture
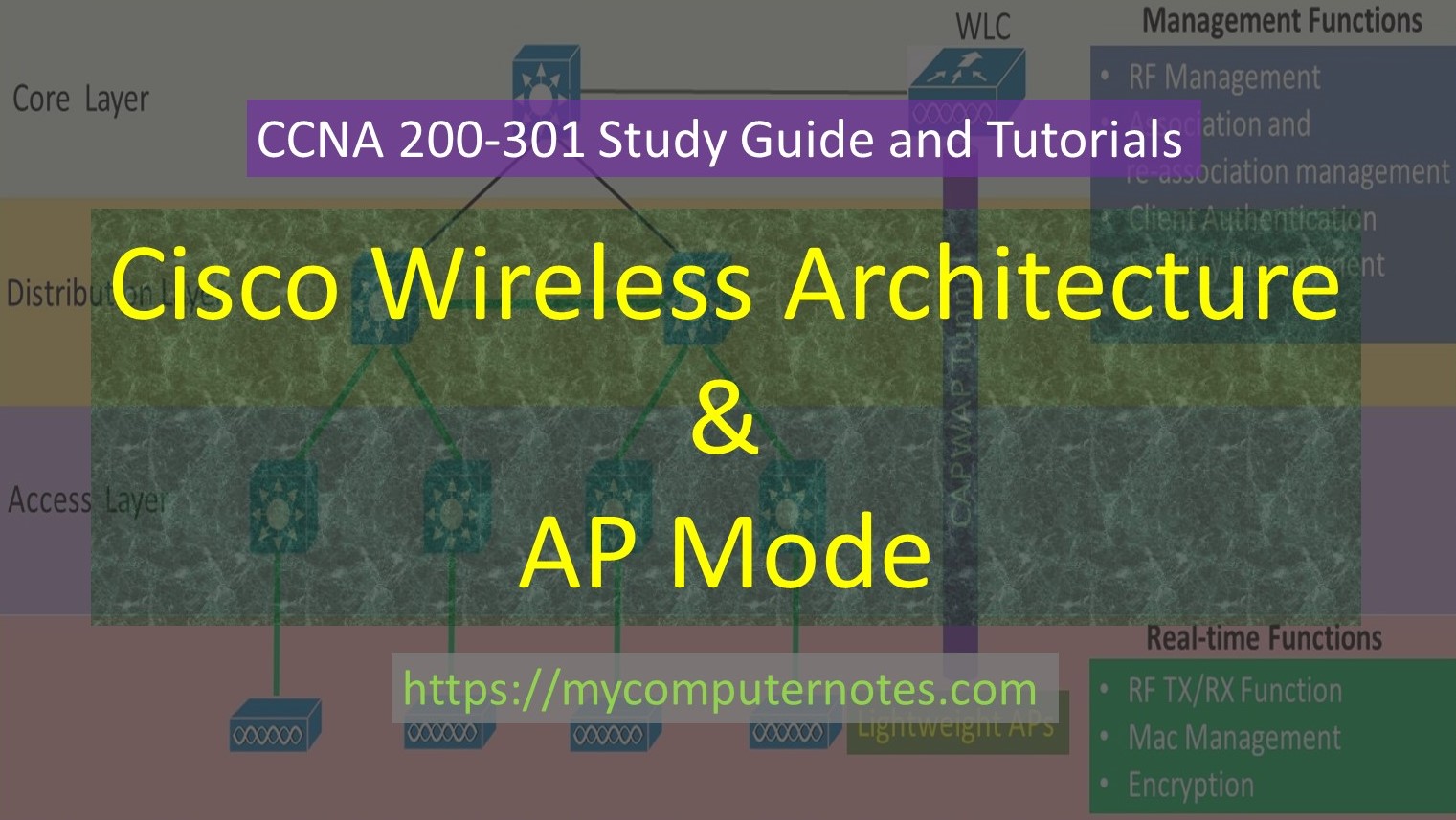
In split-mac AP Architecture, the functionalities of an autonomous AP is divided into two separate functions – The management function and the real-time function.
The management function involves authentication of the client, security management, roaming services, and Quality of Services (QoS). The management function is managed by a centralized wireless LAN Controller (WLC). The WLC has the capability of controlling all the lightweight access points.
The real-time function includes RF transmission of 802.11 frames, MAC management, and encryption. The real-time function is managed by an access point using the protocol called a lightweight access point (LWAP).
In split Mac architecture, every AP is dependent on WLC. Every IP must boot and bind itself with a client support system.

CAPWAP (Controlling And Provisioning of Wireless Access Point)
The tunneling protocol CAPWAP ( Controlling And Provisioning of Wireless Access Point) is implemented between WLC and AP to carry wireless client data and 802.11-related messages.
The CAPWAP protocol encapsulates the data between the wireless controller and access point with new IP packets and can be switched to different VLANs and SSIDs. The CAPWAP tunneling allows the AP and wireless controller to be separated geographically and logically. The CAPWAP breaks the dependence on layer 2 connectivity between them. The CAPWAP tunnel exists between the IP address of WLC and the Access Point packet that is to be routed at the network layer (layer 3).
As the wireless network expands, the WLC builds more CAPWAP tunnels to reach more access points. The CAPWAP tunneling actually comprises two separate tunnels as follows: CAPWAP control tunnels and CAPWAP data tunnel.
- CAPWAP control tunnel deals with the message related to the configuration and management of access points. They are authenticated and encrypted. It uses UDP port 5246.
- CAPWAP data tunnel deals with the exchange of data packets between wireless clients that are associated with AP. The data packets are not encrypted by default.
AP mode
AP mode stands for Access Point mode, which is the mode of operation for a wireless router. In AP mode, the wireless router acts as an access point for clients to connect to the network wirelessly
Local Mode
It is the default mode of any access point (indoor). In this mode, the devices like desktops, laptops, and smartphones access points provide a connection to the client devices as PCs, laptops, and smartphones for seamless wireless connectivity.
Monitor Mode
In this mode, the access point only listens to and monitors the wireless traffic without transmitting any data.
Flex-Connect Mode
In Flex-connect mode, a remote location AP can switch traffic locally between the SSID and VLAN when the link between the CAPWAP tunnel and the WLC is down or it may have been configured to perform in that way.
Sniffer Mode
In this mode, a dedicated AP is deployed to capture or sniff 802.11 radio signals from the other wireless sources. The captured signals are then forwarded to the system where the network analyzer tools such as WireShark or WildPacket Omnipeek are installed.
Rogue Detector Mode
In this mode, the access point pretends to be a legitimate access point to convince users to connect to it, so that hackers can intercept their traffic and steal sensitive data.
Bridge Mode
In this mode, The two or more APs establish the point-to-point or point-to-multipoint connection between the two networks.
SE-Connect Mode
In this mode, an AP is dedicated and connected to Cisco CleanAir Technology for spectrum analysis. Spectrum analysis tools like Metageek Channelyzer of Cisco Spectrum Expert are used to analyze the collected data from all wireless channels to detect any source of interference.
| ← Prev | Next → | |
| Basic Operations of Rapid PVST+ | What is IP Routing and it’s Types |